Important things to know
Risk assessment is the process of identifying, analyzing, and evaluating risks that could negatively impact an organization's operations, assets, or people. It is the backbone of any effective GRC program.
Think of it this way: a hospital cannot secure patient data without first understanding where the vulnerabilities lie. A fintech startup cannot comply with payment card regulations without identifying which systems handle cardholder data. Risk assessment provides that clarity.
From a regulatory standpoint, most major compliance standards : ISO 27001, SOC 2, GDPR, PCI DSS and HIPAA; require organizations to perform documented, repeatable risk assessments. This means that as a GRC professional, mastering risk assessment is not optional. It is foundational.
The Core Risk Assessment Process
Regardless of which framework an organization adopts, most risk assessments follow a similar lifecycle. Understanding this lifecycle helps you apply any framework confidently.
Step 1: Asset Identification
You cannot protect what you do not know exists. The first step involves identifying and documenting all organizational assets, systems, data, personnel, processes, and third-party dependencies.
Step 2: Threat Identification
Next, you identify potential threats to those assets. Threats can be external (cybercriminals, nation-state actors, natural disasters) or internal (disgruntled employees, accidental data deletion, system misconfigurations).
Step 3: Vulnerability Assessment
Vulnerabilities are weaknesses that threats can exploit. This step involves reviewing technical controls, policies, processes, and human behaviours to find gaps.
Step 4: Risk Analysis
Here, you combine threat likelihood with potential impact to determine the overall risk level. This can be done qualitatively (using descriptors like High/Medium/Low) or quantitatively (using numerical values and financial impact modelling).
Step 5: Risk Evaluation and Prioritisation
Not all risks are equal. This step involves comparing identified risks against the organization's risk appetite and tolerance to determine which risks require immediate action and which can be monitored.
Step 6: Risk Treatment
Once risks are prioritised, the organization decides how to address them. Common treatment options include:
- Mitigate
- Accept
- Transfer (e.g., through insurance or outsourcing
- Avoid
Step 7: Monitoring and Review
The risk landscape is constantly evolving. Frameworks mandate periodic reviews to ensure that controls remain effective and that new risks are captured.
Major Risk Assessment Frameworks Explained
Let's now walk through the most widely used risk assessment frameworks. Each has its strengths, its typical use cases, and its nuances. Understanding them will help you choose the right tool for the right job.
1. NIST Risk Management Framework (RMF)
Developed by the National Institute of Standards and Technology (NIST), the RMF is one of the most comprehensive frameworks available. It is widely used across US federal agencies and is increasingly adopted in the private sector globally.
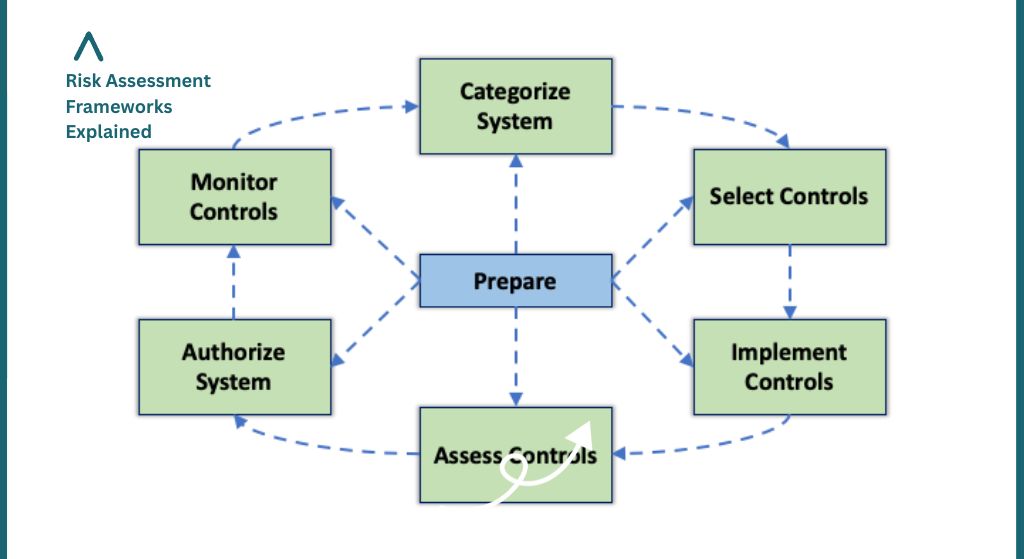
The NIST RMF is built around six core steps:
- Categorise the information system based on impact level
- Select appropriate security controls from NIST SP 800-53
- Implement the selected controls
- Assess whether the controls are implemented correctly and operating as intended
- Authorise the system to operate based on an acceptable level of risk
- Monitor controls on an ongoing basis
The framework is supported by companion publications including NIST SP 800-30 (Guide for Conducting Risk Assessments) and NIST SP 800-37 (RMF for Information Systems). For GRC professionals, familiarity with these documents is highly valuable.
2. ISO/IEC 27005:2022 - Information Security Risk Management
ISO/IEC 27005 is the international standard that provides guidelines for information security risk management. It sits within the broader ISO/IEC 27000 family of standards and is directly linked to ISO/IEC 27001, which defines the requirements for an Information Security Management System (ISMS).
Key characteristics of ISO 27005:
- It is process-oriented rather than prescriptive. It tells you what to do, not exactly how to do it, giving organizations flexibility
- It supports both qualitative and quantitative risk analysis approaches
- It integrates tightly with ISO 27001 controls (Annex A), making it the natural choice for organizations pursuing ISO 27001 certification
- It emphasises risk communication and consultation as ongoing activities
If your organization is working toward ISO 27001 certification or if you're an intern on a project that involves an ISMS audit ISO 27005 is the framework you will likely be applying, whether or not you realize it immediately.
3. OCTAVE (Operationally Critical Threat, Asset, and Vulnerability Evaluation)
OCTAVE was developed by Carnegie Mellon University's CERT Coordination Center and takes a distinctly business-focused approach to risk assessment. Unlike NIST or ISO frameworks, OCTAVE starts with organisational priorities and operational concerns, rather than technical controls.
There are several variants of OCTAVE:
- OCTAVE: the original, comprehensive version for large organizations
- OCTAVE-S: a streamlined version for smaller organizations with limited resources
- OCTAVE Allegro: focuses specifically on information assets and can be conducted without broad organisational participation
The OCTAVE approach is particularly useful when you need to align security risk with business objectives and communicate risk in language that executive leadership understands. It empowers business units and not just IT, to participate meaningfully in the risk process.
4. FAIR (Factor Analysis of Information Risk)
FAIR is a quantitative risk framework that has grown significantly in popularity among CISOs and risk executives. Unlike qualitative frameworks that use labels like 'High' or 'Medium', FAIR enables analysts to express risk in financial terms, answering the critical boardroom question: 'How much could this actually cost us?'
FAIR breaks down risk into two core components:
- Loss Event Frequency (LEF): how often a loss event is likely to occur
- Loss Magnitude (LM): how much loss a single event would produce
By modelling these components using ranges, FAIR produces risk estimates expressed as probable financial loss over a given time period. This is enormously powerful when presenting risk to non-technical stakeholders who think in terms of budget and ROI.
5. COSO Enterprise Risk Management (ERM) Framework
The Committee of Sponsoring Organizations of the Treadway Commission (COSO) developed its ERM framework to address risk management at the enterprise level by going far beyond information security to encompass strategic, operational, financial, and compliance risks.
The updated COSO ERM framework introduced five interconnected components:
- Governance and Culture : establishing tone from the top
- Strategy and Objective-Setting : integrating ERM with strategic planning
- Performance : identifying, assessing, and prioritising risks
- Review and Revision : improving enterprise risk management over time
- Information, Communication, and Reporting : ensuring relevant information flows throughout the organisation
COSO ERM is particularly relevant for GRC professionals who work at the intersection of compliance, audit, and enterprise strategy. It is widely referenced in internal audit and corporate governance contexts.
Framework Comparison at a Glance
Choosing the right framework depends on your organisation's size, industry, regulatory environment, and maturity. The table below summarizes the key differentiators:
How to Choose the Right Framework
A question we hear frequently from interns and junior analysts is: 'Which framework should I recommend?' The honest answer is that there is rarely a single correct answer. In practice, many organisations blend elements from multiple frameworks. However, some guiding principles can help:
- Follow the regulatory requirement first: if your organization must comply with a specific regulation (e.g., ISO 27001, HIPAA, FedRAMP), start with the framework that aligns most directly with that requirement.
- Consider organizational maturity: FAIR, for example, requires data and analytical capability that a new or small organization may not yet have. Start with qualitative frameworks and graduate to quantitative approaches as maturity grows.
- Align with stakeholder language: if your executives speak in financial terms, FAIR or COSO ERM will resonate. If your audience is technical, NIST RMF may be more suitable.
- Think about scalability: OCTAVE-S and simplified ISO 27005 approaches work well for smaller teams. NIST RMF and COSO ERM are designed for larger, more complex environments.
Putting It Into Practice: What This Looks Like in the Field
Theory is important, but GRC is a practical discipline. Here is how a risk assessment typically unfolds in a real engagement:
Scenario: Fintech Startup Preparing for ISO 27001 Certification
You are engaged as a GRC analyst to support a Series A fintech company preparing for their first ISO 27001 audit. They process payments and store sensitive customer financial data.
Your approach would likely draw from ISO/IEC 27005 as the primary framework, given the direct link to ISO 27001. You would:
- Conduct an asset inventory workshop with the engineering and product teams to identify all data stores, systems, and third-party integrations
- Map applicable threats from external attacks (phishing, API abuse) to internal risks (poor access management, shadow IT)
- Evaluate existing controls against ISO 27001 Annex A requirements and identify gaps
- Assign likelihood and impact scores to each identified risk using a defined risk matrix
- Present the risk register to senior leadership with prioritised treatment recommendations
- Document everything in a risk treatment plan that feeds directly into the Statement of Applicability (SoA)
This is exactly the type of structured, real-world GRC work that builds the kind of portfolio evidence that gets candidates hired. It is repeatable, documented, and directly tied to a globally recognized standard.
Risk assessment frameworks are the compass by which GRC professionals navigate uncertainty. Whether you are preparing for a compliance audit, supporting a vendor risk review, or building out an organisation's first ISMS, the frameworks covered in this post give you a structured, defensible way to approach the work.
The professionals who stand out in GRC roles are not those who simply know the frameworks by name. They are those who understand why each framework exists, what problem it solves, and how to apply it pragmatically in the context of a real organisation with real constraints.
Want to learn about how to get started as a GRC professional? Then the Amdari GRC work experience program helps you build your portfolio with projects that have real business impacts and increase your chances of landing jobs. Click this link to book a free clarity call with our team to be guided on what matches your skills best.